Try our Best Antivirus Protection Free for 30 Days
Free Trial DownloadStart your Free 30 day, no credit card needed, no hassle trial today.
Secure your digital life.
Total Defense makes internet security easy for you and tough on destructive malware. We don’t just protect devices, we protect people.
Our software works hard so you don’t have to—no complex questions or specialized knowledge required.
Virus-free. Hassle-free. Worry-free.
Security designed for people, around people.
VB100 Certified
Our virus and malware protection is put through the toughest tests to ensure your are protected.
Learn More >
Free US Tech Support
Our friendly US-based team is standing by to assist with customer care & technical support.
Learn More >
Money Back Guarantee
If you’re not completely satisfied, we’ll refund your money within 60 days of purchase.
Learn More >
Virus-Free Guarantee
We’re so confident in our virus protection, we will remove it for free or give your money back.
Learn More >
Total customer satisfaction is our ultimate goal
Don’t take our word for it…
Protection for all the devices in your home
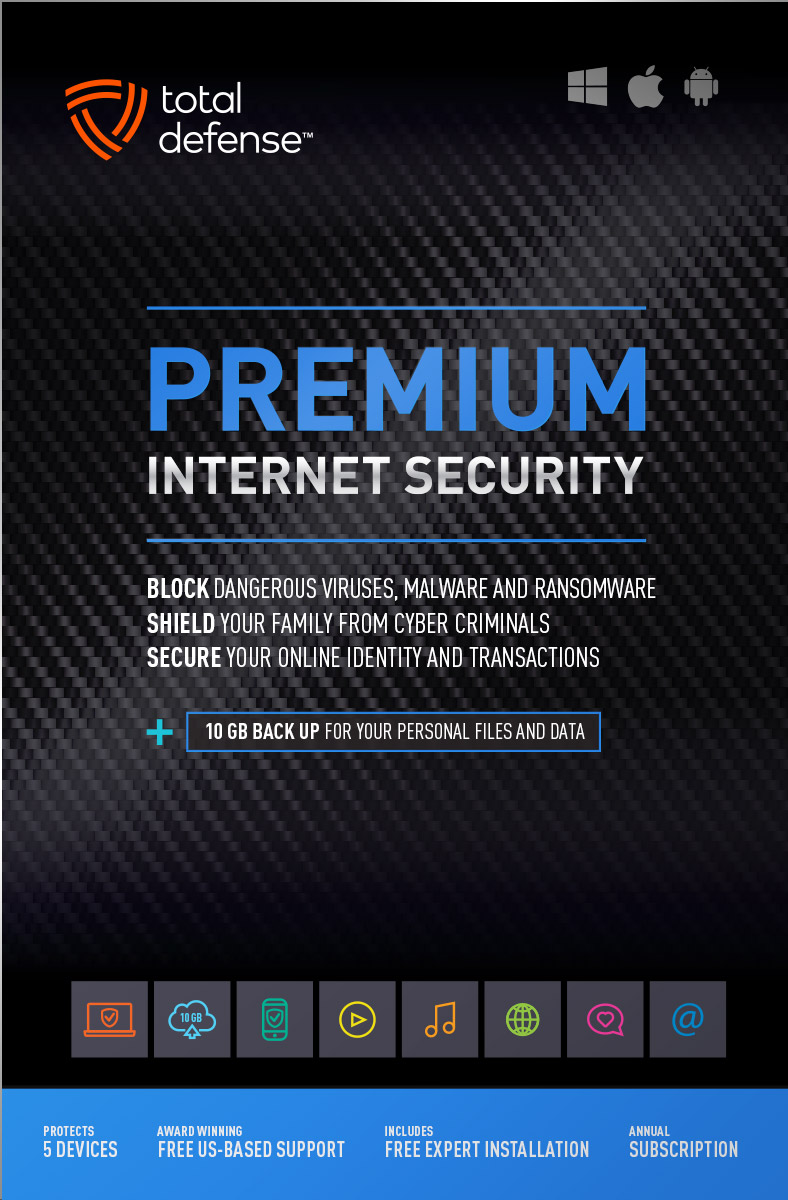
Total Defense
Premium Internet Security

Premium Internet Security provides simple, smart, and reliable protection from viruses, spyware, and malware on up to 5 of your smartphones, tablets, desktops, and laptops.
- Shop, bank and explore your social network without worry
- Protect your information from cyber criminals when you’re shopping and banking online
Our other popular internet security software choices, to keep you and your devices safe.
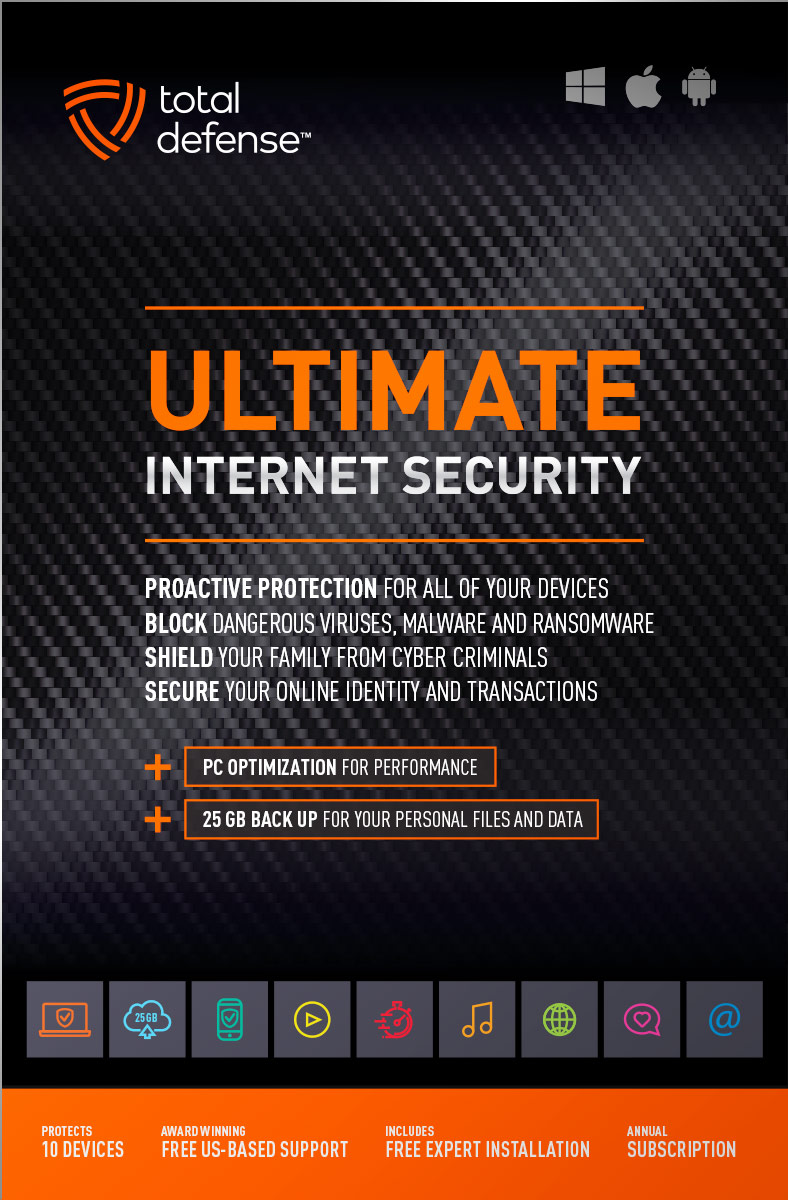
Ultimate Internet Security

Protect everyone on every device in your home - Ultimate is an easy-to-use, all-in-one Internet Security suite that protects you, your family, and up to 10 of your devices from harmful viruses and the latest online threats.
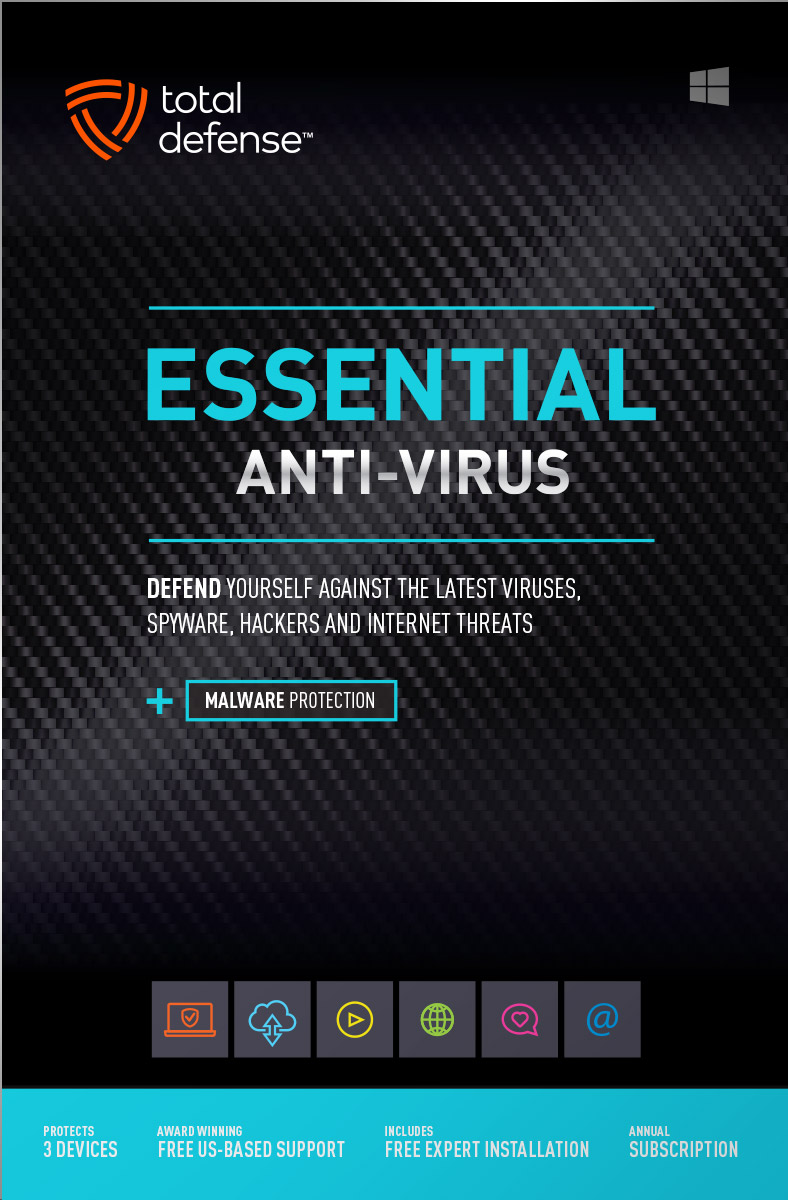
Essential Anti-Virus

Anti-Virus security ensures you’re totally covered keeping your devices safe from malware, spyware, ransomware, and harmful viruses.
Award winning internet security software
Powerful virus detection that doesn’t slow you down.
Learn more about our highly rated malware protection or get started today with a free 30-day trial of Total Defense Internet Security, with no obligation to buy.
Free Trial Download
AV Comparatives Advanced Plus

AV Comparatives Advanced Plus

VB100 Certified

AV Comparatives Advanced Plus

OPSWAT Certified

AV Comparatives Advanced Plus
We will keep you virus-free guaranteed
An exclusive automatic renewal service benefit.
When you choose Total Defense, you’re safeguarded with award-winning, multi-layered virus protection technology. Our powerful security lets you confidently shop, bank and browse online. In fact, we’re so certain we can protect you, if you’re running a Total Defense Security Product and a virus slips past our powerful protection, our expert technology advisors will remove the virus from your device for free. In the unlikely event the virus can’t be removed, we will give you your money back.
»Important terms and offer detailsWe’ve Got You Covered
Over 20 years of Dedication
We are committed to your cybersecurity, from installing the software effectively to helping recovery in the event of a breach.
Advanced Threat Protection
A good offense is the best defense! Real-time and on-demand malware scanning engines provide powerful proactive protection.
Award Winning Security
Powerful protection, securing all entry points, wherever you are, whatever type of device you’re using to access the internet.
Customer Commitment
Our US-based support team is focused on keeping you and your family safe in the ever changing connected world.
Why Total Defense Internet Security >Defend the Defenseless
Total Defense has been a proud supporter of the National Center for Missing & Exploited Children for over 15 years.
Total defense has supported NCMEC in it’s mission to help find missing children, reduce child sexual exploitation and prevent child victimization. We provide quarterly monitary support for NCMEC’s efforts to provide important programs that assist missing and exploited children nationwide.
To learn more about NCMEC, visit www.missingkids.org or see NCMEC on Twitter and Facebook.

Rated #1 anti-virus software company on ConsumerAffairs.com
Over 2,000 customer reviews
We always strive to create the best customer service experience and our customers agree. Total customer satisfaction is our ultimate goal.
Read reviews from our customers>


Total Defense
Internet Security and Safety Center
Helpful tips and articles with practical steps you can follow to improve your online safety
Total Defense Security Tip of the Day
04.18.24
Don't let your router be a security hole–update your firmware
Your internet router silently works in the background, but keeping its software up-to-date is crucial for online safety. Here's why you should update your router's firmware regularly:
- Outdated Firmware = Security Risk: Just like any device, routers have software called firmware. Outdated firmware can have security vulnerabilities that hackers can exploit.
- Patching the Holes: Firmware updates often include security patches that fix these vulnerabilities, making it harder for hackers to break in.
- Improved Performance: Sometimes, updates can even improve your router's performance, giving you a faster and more stable internet connection.
Updating Your Router Firmware: Easier Than You Think
Updating your router might sound complicated, but it's usually a simple process:
- Find Your Router's IP Address: Look for a sticker on your router with its IP address, typically a number like 192.168.1.1.
- Open Your Web Browser: Type the IP address into your web browser's address bar and press enter. This will log you in to your router's settings page.
- Check for Updates: Look for a section on firmware or updates. If an update is available, follow the on-screen instructions to download and install it.
Updating your router's firmware takes just a few minutes but can significantly improve your online security. Make it a habit to check for updates regularly!
Best practices for protecting your business from ransomware attacks
Questions? Our friendly award winning US-based support team is happy to help and it’s free.
1-877-906-8816 Weekdays 9am – 6pm, Eastern Time USA


60 Day Money Back Guarantee
Money Back Guarantee Program
Total Defense is committed to helping you with your refund. If our product does not meet your expectations for any reason, we will provide a full refund within 60 days of your purchase.
Virus Protection Assurance Program
Virus Protection Assurance Program
An exclusive benefit for customers enrolled in the Automatic Renewal Service.
When you choose Total Defense, you’re safeguarded with award-winning, multi-layered virus protection technology. Our powerful security lets you confidently shop, bank and browse online. In fact, we’re so certain we can protect you, if you’re running a Total Defense Security Product and a virus slips past our powerful protection, our expert technology advisors will remove the virus from your device for free. In the unlikely event the virus can’t be removed, we will give you your money back.
»Important terms and offer detailsFree US-Based Support Team
Need Assistance?
US-Based Support • Weekdays 9am – 6pm, Eastern Time USA
Technical Support
Call 1-866-305-7989
or Email
Free technical support includes:
- Download and installation
- Activation and configuration
- Removal of conflicting AV software
- Updates and upgrades
Customer Care
Call 1-877-906-8816
or Email
Customer care assists with:
- Sales and orders
- Account information
- Renewals
- Refunds
- Rebates
- Billing Inquiries
The VB100 Award
VB100 Certification
The VB100 award is a certification of products which meet the basic standards required to be recognized as legitimate and properly functioning anti-malware solutions.
To display a VB100 logo, a product must:- Prove it can detect 100% of malware samples listed as ‘In the Wild’ by the WildList Organization
- Generate no false positives when scanning an extensive test set of clean samples.
- All this must be done with default, out-of-the-box settings in the VB lab environment.